How PDF Documents Are Manipulated and Common Red Flags
PDFs are convenient and widely trusted, which makes them a prime target for financial and identity fraud. Attackers commonly modify document text, swap images, or edit metadata to create convincing fake invoices and receipts. Look for inconsistencies that are difficult to spot at a glance: mismatched fonts, irregular spacing, uneven alignment of columns, or blurred image areas where a logo or signature was replaced. A legitimate supplier invoice usually has consistent typography and clean alignment; deviations are a red flag.
Technical indicators include suspicious metadata such as creation and modification timestamps that don't align with expected dates, or an author field that is blank or inconsistent with the issuing organization. Embedded objects and layers can hide changes — an altered invoice might contain an image of the original with overlaid text edits. Another common trick is copy-pasting text over an area of the PDF so the visible numbers change but underlying OCR or selectable text retains the original values.
Financial red flags are equally important: unexpected changes in banking details, duplicated invoice numbers across different suppliers, or line items with unusually round figures. Check for mismatched totals (for example, line sums not adding up to the stated total), VAT calculations that are off by a small amount, or currencies that don’t make sense for the supplier’s region. Implementing basic cross-checks such as verifying supplier contact details, bank account ownership, and whether the invoice number pattern fits historical records can quickly expose many fraudulent attempts. Emphasizing these visible and behind-the-scenes clues helps teams better detect fake pdf documents before payments are made.
Forensic Techniques and Tools to Verify PDF Authenticity
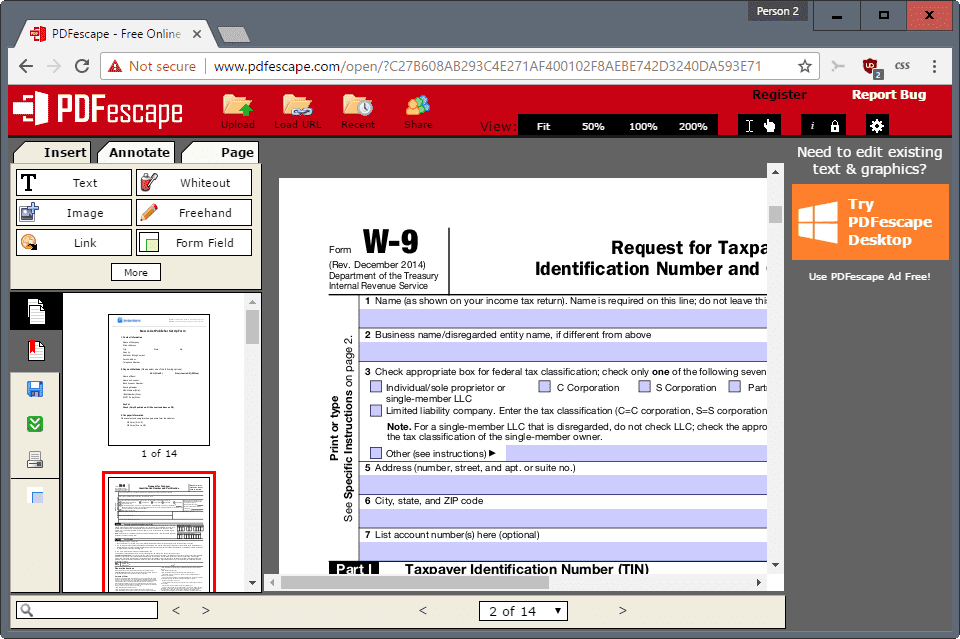
Verifying a PDF’s authenticity combines manual inspection with forensic tools. Start with a simple checklist: open the document in a trusted reader and examine file properties for creation/modification metadata, inspect embedded fonts and images, and use the reader’s search to reveal concealed text or duplicate text layers. Extract the text using OCR to confirm that what is visible matches selectable content, which can reveal pasted-over edits.
More advanced techniques include validating digital signatures and certificate chains. A valid digital signature confirms that contents have not changed since signing and identifies the signer’s credential. Check the signer’s certificate against trusted Certificate Authorities and look at timestamping to ensure the signature was applied when the certificate was valid. Tools like Adobe Acrobat Pro’s “Validate Signature” feature, open-source utilities such as Poppler and QPDF, and metadata viewers can surface anomalies quickly.
Checksum and hashing methods provide deterministic verification: compare a file’s hash with a known-good copy to confirm integrity. For bulk or automated workflows, implement scripting with tools like ExifTool to extract XMP metadata, or use server-side validation APIs to check for structural anomalies. For teams needing a quick, integrated check during invoice processing, specialized services can scan uploaded invoices and receipts to flag irregularities and help detect fake invoice attempts by comparing metadata, visual layout, and data consistency against known patterns.
Real-World Examples, Case Studies, and Prevention Strategies
Case studies show how small lapses in verification enable losses. In one example, a mid-sized company paid a supplier after receiving an invoice with a slightly altered bank account. A quick check of the email header and a phone call to a verified supplier number would have exposed the change; instead, the fraudster intercepted email communications and provided a plausible sounding explanation. In another instance, an employee submitted an expense report with a manipulated receipt image: the totals had been incremented by inserting a small text box over the original subtotal. OCR comparison between the uploaded image and the selectable text revealed discrepancies and stopped the fraudulent reimbursement.
Preventive measures marry process controls with technology. Enforce multi-factor authentication and strict supplier onboarding procedures: verify bank account changes via a known telephone number, require confirmation from a secondary contact, and mandate that high-value invoices be verified with a second approver. Use secure portals for invoice submission rather than email attachments, and require digital signatures for critical documents to reduce the risk of undetected modification.
Train staff to look for behavioral indicators such as urgency cues, requests to change payment details, or subtle pressure to bypass normal approval workflows. Implement automated invoice processing systems that run validation checks — comparing invoice numbers to past records, matching purchase orders, validating VAT numbers, and performing metadata inspections. Regular audits and random sampling of processed invoices can detect patterns and improve detection rules. Combining human skepticism, employee training, and forensic tools creates a layered defense that makes it far harder for attackers to successfully detect fraud receipt or slip fake documents into legitimate workflows.